Every day, businesses and individuals make the dangerous mistake of thinking that formatting a drive or deleting files actually removes sensitive data. In reality, that information remains completely recoverable using basic data recovery software – software that’s available to anyone with an internet connection.
This guide draws from years of experience in secure data destruction to show you exactly why standard deletion methods fail, what certified hard drive destruction really means, and how to choose the right destruction service for your needs.
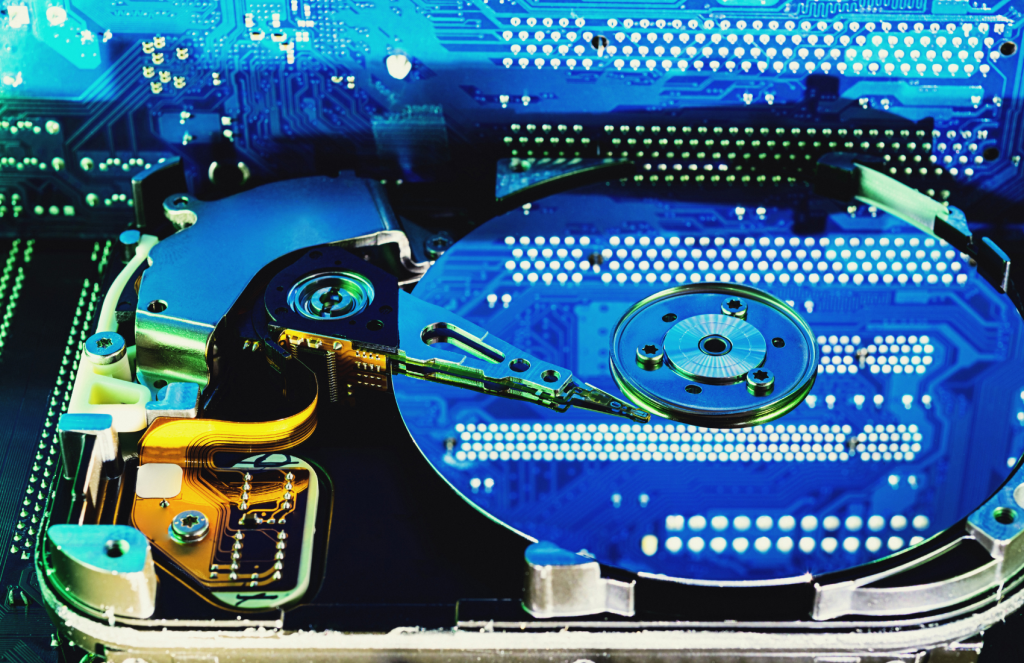
The Hidden Danger in Your Old Computer
Here’s a sobering reality: professional data recovery specialists can retrieve “deleted” files from hard drives in under 30 minutes. We’ve seen it happen repeatedly – businesses thinking they’ve properly wiped drives, only to discover that sensitive information is completely accessible to anyone with basic recovery tools.
Legal and Compliance Requirements
The regulatory landscape around data protection has become increasingly strict:
Healthcare (HIPAA): Improper disposal of patient data can result in fines up to $1.5 million per violation. A single hard drive containing patient records could trigger massive penalties.
Financial Services: Banks face SOX and GLBA requirements that mandate specific data destruction procedures. Non-compliance can result in regulatory action and loss of operating licenses.
State Privacy Laws: California’s CCPA, Virginia’s CDPA, and similar laws require businesses to implement proper data disposal procedures, with significant penalties for violations.
The Real Cost of Data Breaches
According to IBM’s 2023 data breach report, the average cost reached $4.45 million. A regional medical practice faced $2.3 million in costs after patient data was recovered from improperly disposed computers sold at auction – drives that had been “wiped” using standard formatting.
What “Deleting” Actually Does
When you delete a file or format a hard drive, you’re not removing data – you’re simply telling the computer that the space can be reused. The actual data remains physically on the drive until overwritten, which might never happen.
File Deletion: Only removes the directory entry. Data sits untouched until that sector gets reused. Formatting: Creates new file system structure but leaves existing data intact. “Secure Erase”: While better than basic deletion, these commands can fail or not work on damaged drives.
The only guarantee is certified hard drive destruction that physically destroys storage media according to industry standards.
What Certified Hard Drive Destruction Really Means
True certified hard drive destruction follows strict industry standards, provides legal documentation, and uses verified methods that ensure data cannot be recovered under any circumstances.
NIST Standards: The Gold Standard
The National Institute of Standards and Technology (NIST) publishes SP 800-88 Rev. 1, defining three levels of data sanitization. For most business applications involving sensitive data, only physical “Destroy” methods provide adequate security.
Professional Destruction Methods
Industrial Shredding: Most Common Method Professional shredders reduce entire drives to particles no larger than 2mm. These industrial units process hundreds of drives per hour, completely obliterating magnetic platters, electronic components, and cases. The resulting particles are sorted for recycling, but data is gone forever.
Crushing and Mangling Hydraulic systems apply multiple tons of pressure to deform drive platters beyond any possibility of recovery. Platters are bent, twisted, and compressed into unrecognizable shapes through an irreversible process.
Degaussing: Magnetic Erasure High-powered degaussers generate magnetic fields thousands of times stronger than typical magnets, scrambling magnetic alignment that stores data. However, this method:
- Only works on traditional magnetic drives (HDDs)
- Is completely ineffective on solid-state drives (SSDs)
- Often gets combined with physical destruction for maximum security
Incineration: Complete Destruction Reserved for highest security applications, incineration reaches temperatures exceeding 2000°F, providing complete molecular breakdown with zero recoverable remnants.
Certification and Documentation
Chain of Custody: Every drive is tracked from pickup through destruction with tamper-evident seals and witness verification.
Certificates of Destruction: Legally binding documents listing every drive by serial number, destruction method, date, and witness signatures.
Regulatory Compliance: Written verification that methods meet requirements for your specific industry (HIPAA, SOX, GLBA, etc.).
Hard Drive Types and Destruction Challenges
Traditional Hard Drives (HDDs)
Magnetic drives respond well to multiple destruction methods including degaussing, shredding, and crushing. Most contain 2-4 platters that must all be completely destroyed.
Solid State Drives (SSDs): The Modern Challenge
SSDs present unique challenges:
- Magnetic immunity: Degaussing is completely ineffective
- Distributed storage: Data spreads across multiple chips using wear-leveling
- Physical destruction required: Only shredding, crushing, or incineration guarantees complete destruction
Specialized Storage
Hybrid drives, embedded storage, and enterprise arrays each require specific approaches based on their technology and data distribution methods.
The Professional Destruction Process
Step 1: Secure Collection and Inventory
Drives are placed in tamper-evident containers with immediate chain-of-custody documentation. Every drive gets cataloged by serial number, model, and condition.
Step 2: Facility Assessment
Upon facility arrival, drives undergo detailed evaluation to determine appropriate destruction methods based on drive type, client requirements, and regulatory standards.
Step 3: Witnessed Destruction
Professional destruction includes multiple verification steps:
- Client observation opportunities (in-person or video)
- Multiple witness documentation
- Real-time photo/video documentation
- Quality control inspections
Step 4: Post-Destruction Verification
Destroyed materials are verified to meet standards (2mm particle size for shredding), sorted for recycling, and checked for any remaining readable media.
Step 5: Documentation Delivery
Legal certificates listing every drive by serial number are prepared with regulatory compliance attestation and complete chain-of-custody records.
Typical Timeline: 24-48 hours for standard processing, same-day service available for urgent needs.
Choosing a Certified Destruction Provider
Required Certifications
NAID Certification: The industry’s most rigorous standard, covering physical security, destruction procedures, employee background checks, and insurance coverage.
R2 (Responsible Recycling): Ensures environmentally responsible material handling with proper downstream recycling.
ISO 27001: Information security management certification demonstrating systematic data protection approaches.
Facility Standards
Look for:
- Restricted access with surveillance systems
- Industrial-grade destruction equipment
- Environmental controls and safety systems
- Adequate liability insurance ($1 million minimum)
Red Flags to Avoid
- Lack of proper certifications
- Unwillingness to provide facility tours
- Extremely low pricing indicating cut corners
- Poor or incomplete documentation
- Limited insurance coverage
Essential Questions
- “What certifications do you maintain?”
- “Can I witness the destruction process?”
- “How do you maintain chain of custody?”
- “What liability coverage do you carry?”
- “Can you provide industry references?”
Cost Factors and Pricing
Typical Pricing Structure
- 1-10 drives: $8-15 per drive
- 11-50 drives: $6-12 per drive
- 51+ drives: $4-8 per drive
- Enterprise volumes: $3-6 per drive
Additional Services
- Witnessed destruction: 25-50% premium
- On-site destruction: 100-200% premium
- Same-day processing: 100-150% premium
- Drive removal services: $15-25 per system
Cost vs. Risk Analysis
Professional destruction costs ($3-15 per drive) represent minimal expense compared to average data breach costs ($4.45 million) and regulatory penalties (up to $1.5 million per HIPAA violation).
On-Site vs. Off-Site Destruction
On-Site Destruction
Benefits: Complete chain of custody control, real-time witnessing, immediate certificates, maximum regulatory compliance.
Limitations: Higher costs (100-200% premium), equipment limitations, scheduling complexity, minimum volume requirements.
Off-Site Destruction
Benefits: Professional equipment, lower costs, specialized capabilities, environmental controls.
Considerations: Secure transportation required, 24-72 hour processing timeline, facility security standards verification needed.
Choose on-site when: Data sensitivity requires absolute control, regulatory requirements favor it, or internal policies prohibit data leaving premises.
Industry-Specific Requirements
Healthcare (HIPAA)
Requires “appropriate” disposal safeguards with documentation. Physical destruction provides highest assurance for patient data.
Financial Services
SOX and GLBA mandate specific disposal controls. Public companies must maintain destruction controls as part of financial reporting.
Government/Defense
Federal agencies follow NIST guidelines. Defense contractors must meet DoD standards requiring the most stringent destruction methods.
State Privacy Laws
CCPA, CDPA, and SHIELD Act require reasonable security procedures with specific destruction verification requirements.
Protecting Your Organization’s Future
Certified hard drive destruction represents one of the most cost-effective risk mitigation investments available. The typical $3-15 per drive cost is minimal compared to potential breach consequences.
Beyond compliance, professional destruction provides peace of mind. When sensitive data is permanently destroyed according to industry standards, you can focus on business operations instead of security vulnerabilities from old equipment.
Your Next Steps
Immediate Actions:
- Inventory current storage devices containing sensitive data
- Assess disposal practices for adequate security
- Research certified providers using criteria from this guide
- Develop written policies for future storage disposal
Long-Term Planning:
- Establish provider relationships for regular service
- Train staff on proper disposal procedures
- Maintain documentation for compliance audits
- Review policies regularly as technology evolves
The question isn’t whether you can afford certified hard drive destruction – it’s whether you can afford not to securely destroy hard drives containing sensitive information. In today’s threat landscape, proper data destruction isn’t optional – it’s essential for protecting your organization’s future.
Ready to secure your data? Research certified providers, schedule facility tours, and take the first step toward comprehensive data protection. Your stakeholders will thank you for making the right choice. Or, Contact CJD E-Cycling today.